THE NUMBER 1 IN GOVERNANCE, RISK, AND COMPLIANCE MANAGEMENT
Accelerate Detection, Containment, and Recovery With GRC³
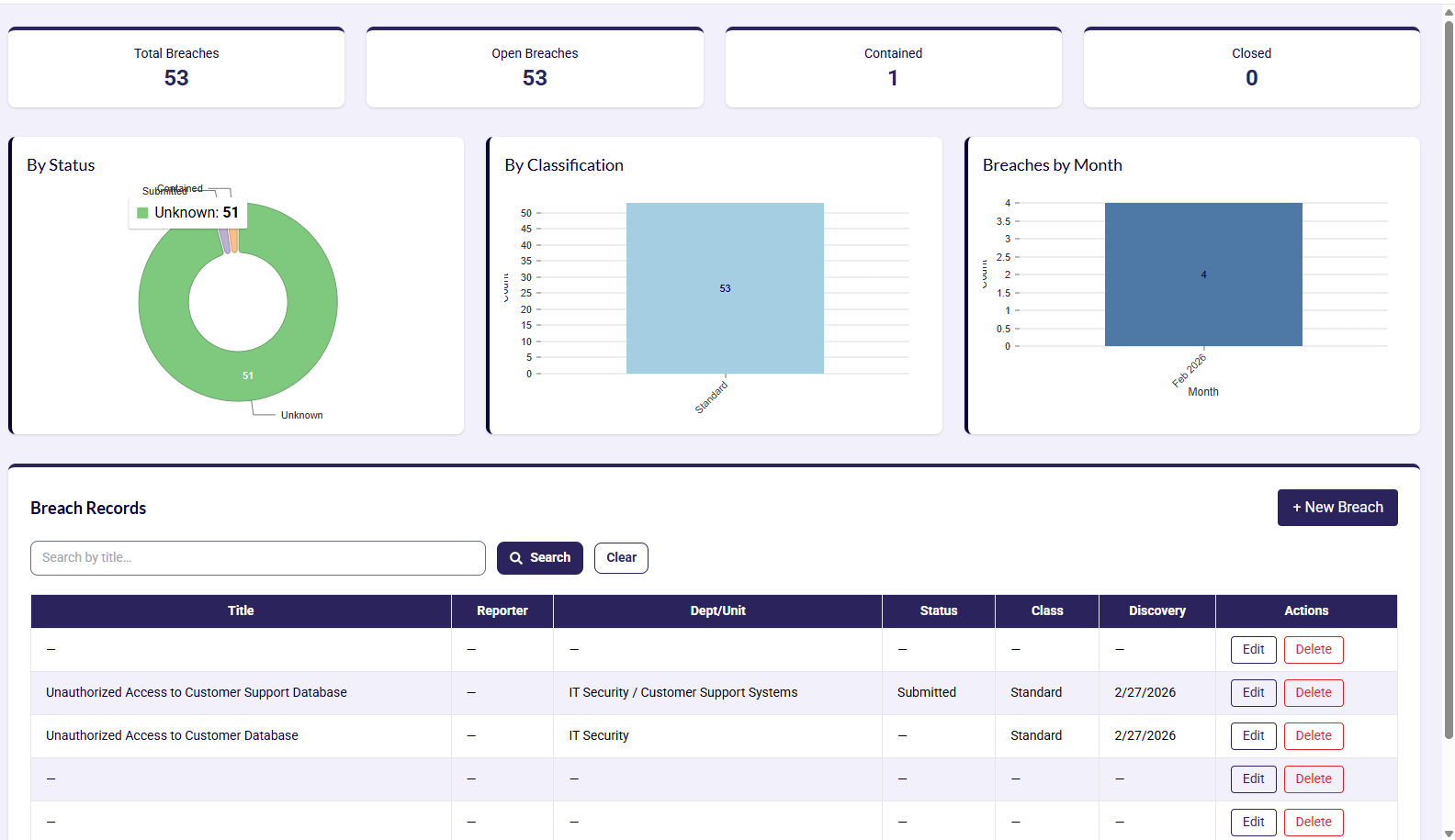
Manage every breach from intake to closure with structured workflows, clear ownership, and real-time visibility to reduce risk impact and improve response confidence.
Why Breach Management?
Track total and open breaches in real time so security teams can prioritize active risk and reduce response delays.
Contain incidents quickly with guided workflows that move cases from detection to a controlled state faster.
Close more incidents with clear ownership, structured evidence, and complete post-incident reporting.
Breach Management
Run breach intake, classification, containment, and closure with one integrated workflow.
Capture Breaches Quickly with Structured Intake
Standardize breach intake with guided forms, mandatory fields, and automatic ticket creation so every incident starts with complete and accurate information.
Centralized Breach Registry
Create one source of truth for all breach records with ownership, timelines, and evidence attached.
Breach Operations Built for Speed, Control, and Clarity.
Live Breach Dashboard
Track total, open, contained, and closed breaches in one dashboard for real-time decision making.
Status and Classification Analytics
Visualize breach trends by status and classification to identify recurring risk patterns quickly.
Monthly Breach Trend Tracking
Monitor breach volume month over month to measure response effectiveness and control maturity.
Searchable Breach Records
Find records instantly with centralized search across title, status, reporter, and discovery date.
Action-Driven Case Management
Handle each case from one workspace with edit, delete, assignment, and review actions.
End-to-End Incident Traceability
Maintain complete traceability of every change from intake to closure to support audits and investigations.
FAQs
Breach management software helps organizations log, classify, investigate, contain, and close security or privacy breaches through one structured workflow. It centralizes evidence, ownership, response tasks, and reporting so teams can respond faster and stay audit ready.