Innovations driving digital transformation and connectivity
Transforming the Future with Technology
Technology is reshaping industries, improving efficiency, and enhancing everyday life through continuous innovation and digital advancements.
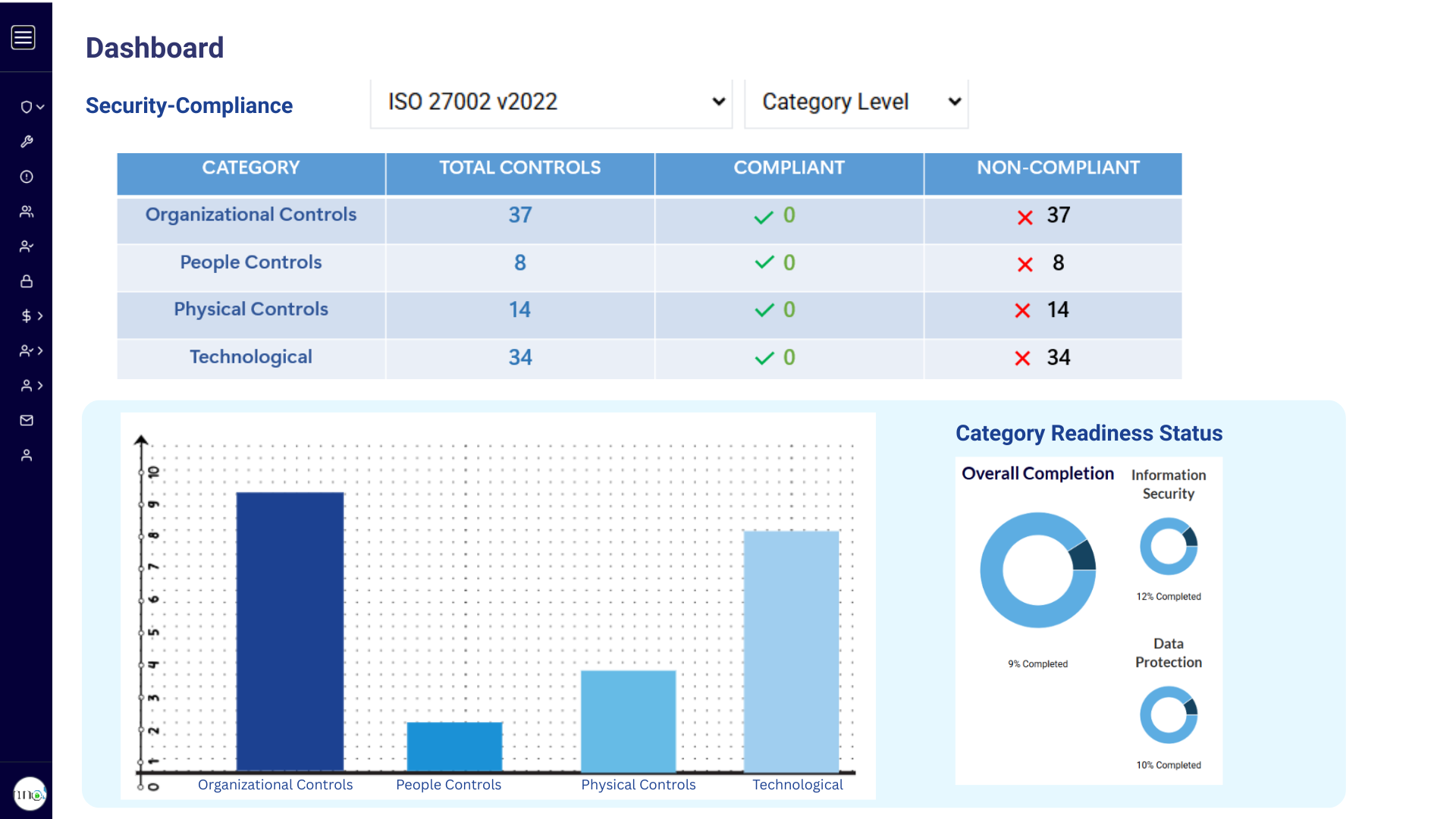
Maintain, Protect, and Reduce Risk with a Compliance and Cybersecurity Strategy
Cybersecurity threats such as ransomware, malware, phishing, and IoT-based attacks continue to evolve, and recent threat intelligence shows organizations facing increasingly sophisticated risk patterns.
Threat Horizon and similar industry reporting highlight three recurring themes organizations need to plan for:
Organizations will continue to face threats such as cloud vulnerabilities, AI-enhanced cyberattacks, AI fuzzing, machine learning poisoning, smart contract hacking, and social engineering. Many of the techniques used by attackers will be unfamiliar, which is why technology teams need to rethink IT security and risk strategy rather than rely on static controls.
- Disruption: the risk of premeditated internet outages that compromise business operations
- Distortion: the spread of misinformation by bots and automated sources
- Deterioration: rapid advances in smart technology combined with conflicting national security demands


Technology
Compliance challenges continue to expand as privacy regulation increases across jurisdictions. Organizations are investing more resources than ever in compliance, while still dealing with a shortage of qualified cybersecurity and compliance professionals.
Organizations need a trusted partner to help them continually enhance security and compliance. e-InnoSec has made significant investments in leadership, methodology, and personnel to serve in that role, with services that include free training through the SECURTEAIN eLearning platform as well as classroom training.
Rethink the Security and Risk Strategy
| Cybersecurity Strategy | Cybersecurity Awareness |
| Strong Authentication | Strong Backup |
| Disaster Recovery | Business Continuity |
| Encryption | Vulnerability Management |
| Data Security and Privacy (GDPR, CCPA, and HIPAA) | Regulatory Compliance and Frameworks - NIST CSF, FISMA, ISO, CSA |
| Pen Test | Digital Transformation |
Programs Built for Technology Risk, Security, and Compliance
GDPR, CCPA, and Privacy State Laws
Support compliance with global and state privacy requirements while strengthening protection of personal data and consumer rights.
SOC 1 and SOC 2 Examination
Prepare for independent audits that evaluate control effectiveness across financial reporting, security, availability, confidentiality, and privacy.
FISMA Compliance
Align security programs to federal requirements and NIST-based expectations for protecting sensitive systems and government-related data.
PCI Compliance
Strengthen controls around cardholder data and payment environments to meet PCI DSS requirements with confidence.
Application Security Assessment
Identify application weaknesses early and improve software resilience with structured security assessments and remediation guidance.
Threat Modelling, Vulnerability Management, and Pen Test
Use a proactive security program to identify, assess, and reduce risk through threat modeling, continuous vulnerability management, and penetration testing.
FAQs
Technology management in GRC refers to managing IT systems, cybersecurity, compliance, and risk through structured frameworks to ensure secure, efficient, and compliant operations across an organization.