 Risk & Compliance
Risk & ComplianceLearn how GDPR preparation creates a foundation for CCPA compliance and where California-specific controls are still required.
Stay ahead with expert analysis about compliance, risk management, DPDP, and cybersecurity news.
 Risk & Compliance
Risk & ComplianceLearn how GDPR preparation creates a foundation for CCPA compliance and where California-specific controls are still required.
 Risk & Compliance
Risk & ComplianceLearn how preparing for GDPR can simplify CCPA compliance for businesses handling both laws.
 Risk & Compliance
Risk & ComplianceLearn the key differences between GDPR and CCPA and how to build a unified compliance strategy.
 Risk & Compliance
Risk & ComplianceWalk through the four DPIA elements, privacy risk analysis, mitigation, and alignment with GDPR and DPDP controls.
 DPDP
DPDPStep-by-step guidance on implementing encryption for DPDP compliance in India.
 DPDP
DPDPLearn how to conduct data inventory and mapping under DPDP compliance and streamline privacy operations.
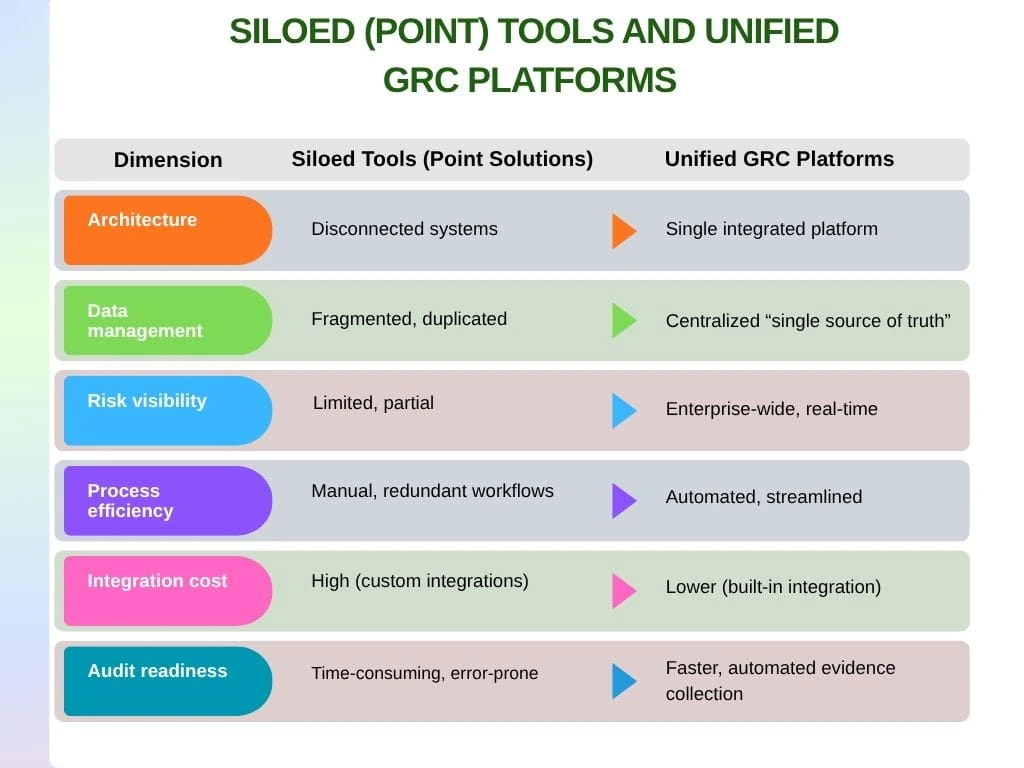 GRC
GRCUnderstand how unified GRC platforms improve governance, risk, compliance, visibility, and control.
 GRC
GRCDiscover how AI is transforming GRC with predictive analytics, real-time decision-making, and automated risk assessments.
 DPDP
DPDPImplement access controls, encryption, and automation to protect personal data and keep DPDP programs audit-ready.
 DPDP
DPDPExplore the shift in DPDP compliance from planning to execution, predictable timelines, and accountability.
 DPDP
DPDPDiscover how a unified platform eliminates fragmented tools and strengthens DPDP and cyber GRC execution.
 DPDP
DPDPLearn how to scale DPDP compliance across territories using unified GRC, AI, and multi-framework strategies.
Explore the insights and trends shaping our industry.

The best ways to protect personal data under the DPDP Act include access controls, encryption, data minimization, risk assessments, continuous monitoring, employee training, vendor risk management, retention controls, incident response planning, and compliance documentation.

Learn to describe processing, assess necessity, evaluate risk, and implement mitigation so your DPIAs drive GDPR/DPDP compliance.

Cyberattacks are detected by continuously monitoring systems, analyzing logs, and correlating unusual behavior with tools like SIEM, EDR, and intrusion detection systems before damage escalates.

Cyberattacks can be prevented by implementing multi-factor authentication (MFA), patching vulnerabilities, securing networks, and training employees. A layered cybersecurity strategy combining Zero Trust, endpoint protection, and continuous monitoring significantly reduces the risk of attacks.