Managing vulnerabilities is one of the biggest challenges in modern cybersecurity programs. As organizations scale, the number of vulnerabilities increases faster than teams can fix them, creating a vulnerability remediation backlog. A manageable vulnerability management program requires risk-based prioritization, strong governance, asset visibility, and continuous tracking of remediation efforts.
This guide explains how to build a scalable, sustainable vulnerability management program aligned with risk management, security governance, and compliance frameworks.
What Is a Vulnerability Management Program?
A vulnerability management program is a continuous process of:
- Identifying vulnerabilities
- Assessing risk
- Prioritizing remediation
- Fixing and monitoring issues
It is a core part of cyber risk management and helps reduce the attack surface of an organization.
Read also: How to Detect CyberattacksI
Why Vulnerability Backlog Is a Major Problem?
Most organizations struggle with a growing backlog of vulnerabilities.
Key Reasons:
- Too many vulnerabilities discovered
- Limited remediation resources
- Poor prioritization strategies
- Lack of ownership
Even with scanning tools, backlogs continue to grow without proper strategy. The problem is not detection - it is prioritization and execution.
Read also: CMMC Introduction - Everything You Need to Know About DoD CMMC
How to Make Vulnerability Management Sustainable?
A sustainable program focuses on people, process, and technology.
Core Approach:
- Understand the root cause of backlog
- Define governance and workflows
- Align with business risk
Organizations must move beyond tools and focus on strategy and decision-making.
Read also: How to Prevent Cyberattacks
Key Strategies to Manage Vulnerability Backlog
1. Why Governance Is Critical in Vulnerability Management
Strong security governance ensures accountability and execution.
Key Governance Elements:
- Defined roles and responsibilities (RACI)
- Asset ownership clarity
- Policy-driven remediation
Lack of ownership is one of the biggest causes of backlog.
Read also: How to Prevent Cyberattacks
2. How Risk-Based Prioritization Improves Security
Not all vulnerabilities are equal.
Risk-Based Approach:
- Focus on critical assets first
- Use CVSS + business context
- Prioritize exploitable vulnerabilities
Modern programs use risk-based vulnerability management (RBVM) to reduce effort and maximize impact.
Read also: Key Risk Indicator and KPI in Cybersecurity Part I
3. Why Asset Inventory Is Essential for Attack Surface Reduction
You cannot secure what you don't know.
Asset Inventory Benefits:
- Identifies unknown assets
- Improves visibility
- Reduces attack surface
Attackers often exploit unmonitored or unknown systems. Asset inventory helps detect hidden risks and prevents attackers from exploiting unknown assets.
Read also: Examples of Effective KRIs Part III
4. How Prioritization Reduces Vulnerability Risk Faster
Effective prioritization depends on:
- Asset criticality
- Threat intelligence
- Exploitability
Without prioritization, teams waste time fixing low-risk issues. Focus on high-risk vulnerabilities first to reduce impact quickly.
Read also: Breach Management Guide Part II
5. Why Centralized Command Improves Response
A centralized vulnerability management system ensures:
- Faster decision-making
- Consistent remediation
- Better coordination
A clear chain of command improves response efficiency.
Read also: How Malware Infection Happens
6. How Tracking and Communication Improve Remediation
Tracking vulnerabilities is critical for success.
Key Practices:
- Track remediation status
- Use dashboards and reports
- Define KPIs (MTTR, SLA)
Communication between teams reduces delays and improves outcomes.
Read also: How to Protect Against Malware Part IV
7. How to Reduce Attack Surface in Cybersecurity
Reducing attack surface is one of the most effective strategies.
Key Actions:
- Remove unused applications
- Restrict access
- Harden configurations
- Secure endpoints
Attack surface includes all systems, applications, and interfaces exposed to users.
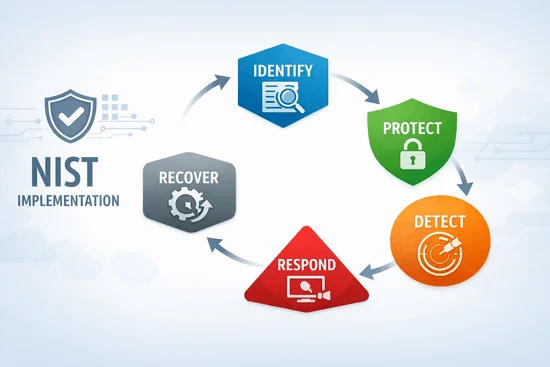
Read also: NIST Implementation Guide
What Role Does Threat Modeling Play in Vulnerability Management?
Threat modeling helps organizations identify risks before they occur.
Popular Models:
- STRIDE
- PASTA
- LINDDUN
- Attack Trees
Threat modeling enables proactive security design and reduces vulnerabilities early.
Read also: SOAR and Threat Intelligence Part II
What Are the Key Components of an Effective Program?
Based on competitor and industry analysis:
Essential Components:
- Continuous vulnerability scanning
- Risk-based prioritization
- Automated remediation workflows
- Security monitoring
- Reporting and compliance tracking
Modern programs also integrate:
- SOAR (automation)
- SIEM (monitoring)
Read also: AWS and Azure Cloud Security Part II
Conclusion
Building a manageable vulnerability management program requires more than tools - it requires strategy, governance, and continuous improvement.
Organizations that:
- Prioritize risks effectively
- Track remediation performance
- Maintain asset visibility
- Reduce attack surface
can significantly improve cyber resilience and security outcomes.
The key is not fixing everything - it is fixing what matters most first.
If you would like guidance on strengthening your DPDP compliance framework or understanding how governance, risk, and compliance tools can support your organization, feel free to contact us for assistance.
You can also visit our website to explore how modern GRC platforms help organizations manage data protection, risk management, and regulatory compliance in a more structured and scalable way.
FAQ
It is the process of identifying, assessing, prioritizing, and fixing vulnerabilities to reduce security risks.
Related Posts