Access management is one of the most critical areas of cybersecurity in 2026. As organizations move to cloud systems, remote work, mobile devices, and third-party integrations, traditional login methods like passwords and static multi-factor authentication are no longer enough. Risk-based authentication is an adaptive security method that evaluates login risk in real time and applies stronger verification only when needed. This approach helps organizations improve security while maintaining user convenience.
Risk-based authentication is an adaptive access method that compares the risk level of a login attempt with the acceptable risk threshold of the target system. Based on the result, the system may allow access, request additional verification, or block the login attempt.
One of the most important security domains is Access Management. Over time, authentication methods have evolved from simple passwords to secure tokens, PINs, OTP apps, biometrics, and behavioral authentication.
As businesses continue to adopt cloud services, BYOD, remote work, and external partners, the number of users accessing systems has increased significantly. This growth also increases the attack surface and creates more opportunities for cybercriminals.
Because of these risks, many organizations in 2026 are adopting risk-based authentication instead of relying only on traditional multi-factor authentication.
This article is useful for auditors, risk management professionals, information security teams, operations staff, business managers, and legal teams.
What is risk-based authentication and why is it used?
Risk-based authentication compares the risk score of a user with the risk threshold of the system they want to access.
- If the risk level is low → access is allowed
- If the risk level is medium → additional verification required
- If the risk level is high → access denied
Extra verification may include:
- SMS OTP
- Authenticator app
- Biometric verification
- Security questions
- Email verification
This method reduces unauthorized access while keeping login simple for trusted users.
Read also:- IoT Devices A High-Security Risk
How is a user risk score evaluated?
A user risk score is calculated using different factors such as:
- Login device
- User identity
- Location / IP address
- Time of login
- User behavior history
- Job role or privilege level
- Known attack patterns
Modern systems also use behavioral analytics to learn normal user activity and detect unusual login attempts.
Adaptive authentication combines static rules and behavior learning to create better protection.
What is a system risk threshold?
Each system has a defined risk threshold based on the sensitivity of the data stored.
Factors used to define threshold:
- Data classification
- Business impact of breach
- Confidentiality requirements
- Integrity requirements
- Availability requirements
Systems with financial data, personal data, or intellectual property should have very low risk tolerance.
Read also:- Breach Management Part II
How do user risk and system threshold work together?
Risk-based authentication compares the user risk score with the system risk threshold.
Examples:
- Low-risk user + low-risk system → allow
- Medium risk + sensitive system → extra verification
- High risk + sensitive system → deny access
This prevents attackers from accessing critical systems even if they know the password.
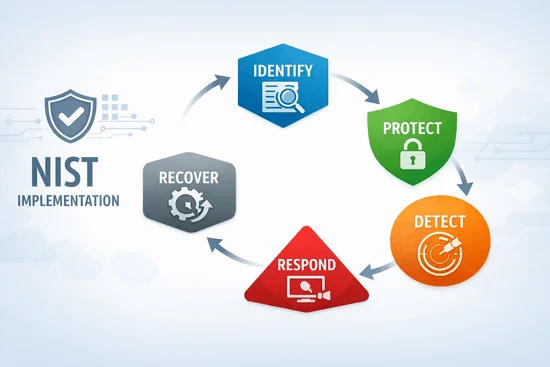
What does the risk-based authentication diagram show?
The risk-based authentication model shows how access decisions change based on risk level.
- Acceptable risk → Pass
- Medium risk → Step-up authentication
- High risk → Fail / Block
This adaptive approach is more secure than static authentication.
Conclusion
In 2026, organizations cannot rely only on passwords or basic multi-factor authentication. Risk-based authentication provides smarter protection by analyzing user behavior, device, location, and system sensitivity before allowing access. This method reduces unauthorized access, improves security, and helps organizations protect sensitive data without slowing down trusted users. Adaptive authentication is becoming a key part of modern identity and access management strategies.
FAQs
Risk-based authentication is a security method that checks the risk level of a login attempt and decides whether to allow, verify, or block access.
Related Posts